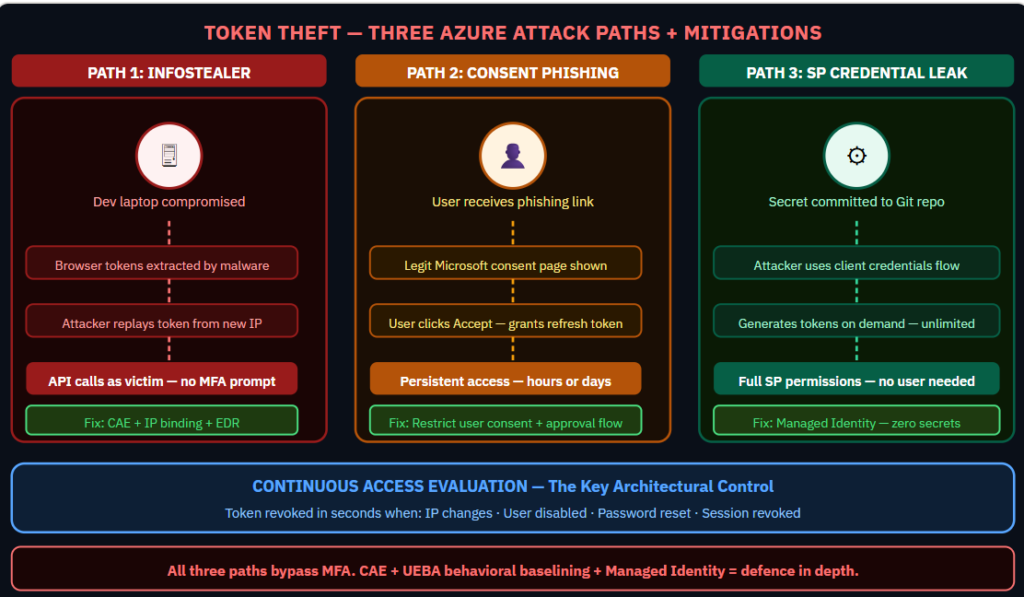
When an attacker steals an access token, credentials and MFA become irrelevant. The token is valid. The session is trusted. The attacker looks identical to the legitimate user because they are carrying the legitimate user’s proof of authentication. MITRE ATT&CK T1528 — Steal Application Access Token — is one of the most underdetected techniques in Azure environments. Three paths lead to it. Each has different detection signals and different mitigations. The path that most organizations have no detection for at all:
All three token theft paths mapped end-to-end, the Sentinel KQL rules that catch each one, and why Continuous Access Evaluation is the single most impactful control most teams have not enabled.
Why Token Theft Matters More Than Credential Theft
Password compromise requires the attacker to authenticate and potentially trigger MFA. Token theft skips all of that. A stolen access token is proof that authentication already happened. The bearer of the token is trusted by the resource. Entra ID has no way to know the legitimate user is not holding it.
The average token lifetime for Microsoft Graph is 60–90 minutes. A refresh token can generate new access tokens for hours or days depending on the configuration. This is the window attackers exploit.
Attack Path 1: Infostealer Malware on Developer Endpoint
Infostealer malware extracts session cookies and cached tokens from browser storage on a compromised developer laptop. The attacker imports those tokens into their own browser using tools like Cookie-Editor or custom scripts. From Entra ID’s perspective, the session is continuing from the same token that was legitimately issued.
Detection signal: no new authentication event occurs. The only observable difference is an IP address change. If the attacker uses a residential proxy in the same city, even this signal disappears.
Mitigation: Continuous Access Evaluation with strict location enforcement. CAE allows token revocation to propagate to CAE-enabled resource servers in near-real time when IP context changes significantly. Enable it for all high-sensitivity applications. Combine with device compliance enforcement — a compliant device cannot easily run infostealer malware without detection by the EDR.
Attack Path 2: OAuth Consent Phishing
The attacker registers a malicious app in any Entra ID tenant (including a free one) and crafts a URL that requests OAuth delegated permissions from the target user. The user is redirected to a legitimate Microsoft consent prompt. If they click Accept, the malicious app receives a refresh token for the user’s permissions. The attacker now has persistent delegated access without needing the user’s password or MFA code.
Detection signal: an OAuth consent grant appears in the Entra ID audit log. Most organizations do not alert on this. The event looks like any other application authorization.
Mitigation: restrict user consent to applications from verified publishers or disable user consent entirely and require admin approval. Use Entra ID’s permission classification policy to block consent to high-risk API permissions at the user level. Enable the admin consent workflow so users who need to grant permissions are routed to an approval process rather than blocked outright.
Attack Path 3: Over-Privileged Service Principal Credential Leak
A service principal credential appears in a Git repository, a pipeline log, a container image, or an error message. The attacker uses the client credentials OAuth flow to obtain access tokens with the full scope of the service principal’s permissions. No user is involved. No MFA is triggered. The tokens are generated on demand as long as the credential is valid.
Detection signal: client credentials flow authentication events from an unusual IP or geographic location. Behavioral anomaly if the call patterns differ from the service’s established baseline.
Mitigation: replace all service principal client secrets with Managed Identity where supported. For service principals that cannot use Managed Identity, use certificates rather than client secrets and store them in Key Vault with auto-rotation. Enable Sentinel UEBA to baseline service principal behavior and alert on deviations.
Continuous Access Evaluation — The Most Impactful Underused Control
Standard OAuth tokens are valid until they expire. CAE allows resource servers to reject tokens mid-session when specific events occur: user account disabled, password changed, session revoked, IP address changes significantly, MFA registration changed. These events are communicated to CAE-aware resource servers in near-real time, reducing the exploitation window from 60 minutes to seconds.
CAE is enabled by default for many Microsoft services. Verify which applications in your environment support CAE, and ensure it is active for your highest-sensitivity workloads.
KQL: Detect Token Use From New Geography
This query identifies sign-ins using tokens from countries not seen for that user in the past 30 days:
SigninLogs | where TimeGenerated > ago(1h) | extend Country = tostring(LocationDetails.countryOrRegion) | join kind=leftanti (SigninLogs | where TimeGenerated between(ago(30d)..ago(1h)) | summarize HistoricCountries=make_set(tostring(LocationDetails.countryOrRegion)) by UserPrincipalName | mv-expand HistoricCountries | project UserPrincipalName, Country=tostring(HistoricCountries)) on UserPrincipalName, Country
More information:
https://learn.microsoft.com/en-us/entra/identity-platform/security-best-practices-for-app-registration
#EntraID #TokenTheft #AzureSecurity #MITRE #IdentitySecurity