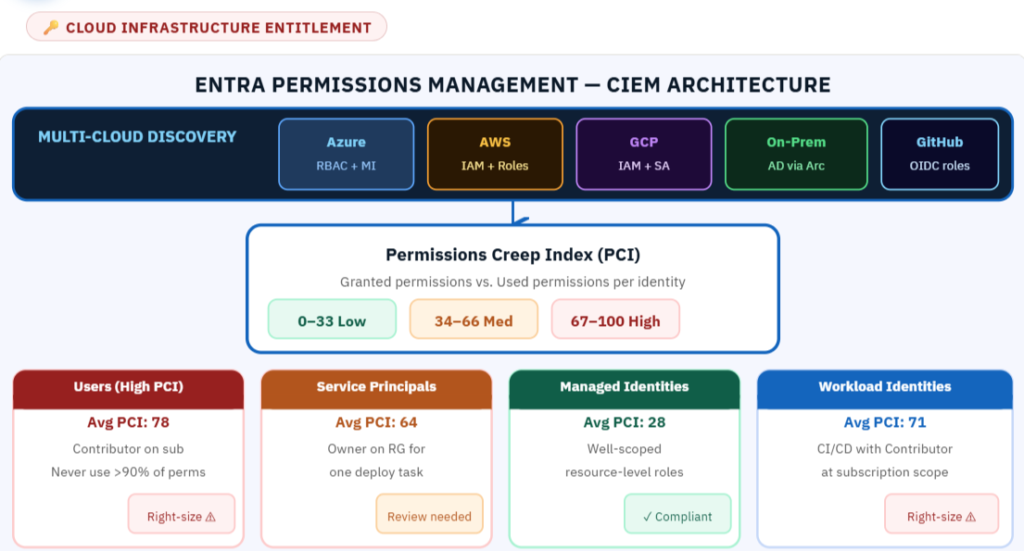
In every Azure environment I review, identities have 10× the permissions they actually use. That gap is the blast radius.The average cloud identity uses less than 5% of the permissions it has been granted. The other 95% sits idle — unused, unmonitored, and available to any attacker who compromises that identity. This is the Cloud Infrastructure Entitlement Management (CIEM) problem. It is not about who has access. It is about the gap between who has access and who actually uses it. Microsoft Entra Permissions Management addresses this at scale across Azure, AWS, and GCP. Three metrics drive everything: Permissions Creep Index (PCI) — a score from 0 to 100 for every identity. A score of 85 means that identity has been granted permissions far beyond what it uses. Here is what I see when I run PCI analysis in a first-time deployment:
What Cloud Infrastructure Entitlement Management Actually Solves
CIEM is not about denying access. It is about understanding the gap between what identities are permitted to do and what they actually do, then systematically closing that gap to reduce blast radius.
When an identity is compromised — through credential theft, token replay, or malware — the damage the attacker can do is bounded by the permissions that identity holds. A compromised Contributor identity on a subscription gives an attacker 600+ permissions across every resource in that subscription. A compromised identity with a custom role scoped to one resource group gives an attacker access to exactly that resource group.
CIEM makes the second scenario the default.
The Permissions Creep Index
The PCI is Microsoft Entra Permissions Management’s primary metric. It measures, for each identity, the ratio of permissions granted to permissions actually used over the past 90 days. An identity with PCI 85 has been granted permissions for which 85% have never been exercised.
When you run Entra Permissions Management against a real environment for the first time, the average PCI for human identities is typically above 70. Service principals are often worse because they were provisioned with broad permissions to “make the deployment work” and nobody refined them afterward. Managed identities tend to score better because they are created with a specific technical purpose and their permissions are reviewed during deployment.
The Right-Sizing Workflow
Entra Permissions Management’s right-sizing recommendation generates a custom role definition that contains only the permissions the identity actually used in the past 90 days, plus a configurable buffer for permissions that are used infrequently but are genuinely needed.
The workflow: identify identities with PCI above threshold (I use 60 as the trigger). Review the right-sizing recommendation. For service principals and managed identities, the recommendation can often be deployed directly. For human identities, the recommendation requires review against the identity’s documented job function before deployment.
Continuous Monitoring and Drift Prevention
Permissions creep recurs. A right-sized identity gets a broader role because a ticket came in requesting access. Six months later the expanded access is no longer needed but it was never removed. Entra Permissions Management can alert when a previously right-sized identity’s PCI crosses a threshold again, creating a governance loop that catches drift before it compounds.
Set PCI alerts at 60 for service principals and workload identities, 70 for human users. Weekly review the alert list. Require documented justification for any identity whose PCI increase is approved rather than remediated.
Cross-Cloud Value
The same PCI analysis that applies to Azure RBAC applies to AWS IAM policies and GCP IAM bindings through the multi-cloud connector. An organization that runs workloads across all three clouds can see a unified permissions posture view and identify the identities with the highest blast radius regardless of which cloud they operate in.
For more information, check out the link below:
https://learn.microsoft.com/en-us/entra/permissions-management/overview
https://learn.microsoft.com/en-us/entra/permissions-management/overview
#CIEM #EntraPermissionsManagement #LeastPrivilege #AzureSecurity #MVP
Be the first to comment
Leave a Comment
💡 Comments are reviewed before publishing.